Penetration test, often called “penetration testing or pen testing,” is a simulated cyberattack against your systems to identify security vulnerabilities before real attackers do. The goal is to uncover potential entry points and weak spots that could be exploited to access sensitive data, disrupt operations, or damage reputation. Pen testing is a critical part of modern cybersecurity strategies, as it provides insight into the effectiveness of existing security controls and helps organizations take corrective actions before actual harm is done.
At CyberSafe, we approach penetration testing not as a checklist exercise, but as a strategic management discipline that quantifies risk in business terms. Our assessments evaluate the genuine effectiveness of your existing security controls, uncover potential entry points that could enable data exfiltration or operational disruption, and translate technical findings into the executive language of risk, cost, and resilience.
The fundamental distinction between our methodology and commodity testing lies in intent. Where most providers deliver volume-based vulnerability reports, we deliver decision-grade intelligence — the kind of insight that supports board reporting, regulatory submissions, and capital allocation decisions for cybersecurity investment.
The Core Value: CyberSafe transforms penetration testing from a technical audit into a strategic management tool. Our certified Red Team — holding OSCP, CEH, CISSP, and PenTest+ credentials — simulates real-world attack chains that automated scanners cannot replicate. Across hundreds of engagements with financial institutions, healthcare providers, fintech innovators, and critical infrastructure operators, we have consistently uncovered the systemic risks that determine whether an organization survives a breach or becomes the next cautionary headline.
Why Your Organization Needs a CyberSafe Assessment?
In today’s threat landscape, no organization is too small to attract attackers and no system is too obscure to be probed. A modern breach is rarely confined to stolen data: it cascades into operational paralysis, contract loss, regulatory penalties, and lasting reputational damage. Industry research consistently shows that the majority of breached small and mid-sized organizations never fully recover. The cost of prevention is always lower than the cost of incident response, customer notification, and legal exposure combined.
Our Strategic Management Approach:
- Beyond Automated Tools: While scanners identify symptoms, our experts diagnose the root cause of systemic vulnerabilities — including chained exploits and business logic flaws.
- Regulatory Alignment: We design engagements to satisfy the rigorous requirements of ISO 27001, SOC 2, DORA, HIPAA, PCI-DSS, and GDPR audits.
- Operational Resilience: We evaluate not only your technology stack but also your security team’s capacity to detect, contain, and recover from simulated intrusions.
- Executive Clarity: Every engagement concludes with prioritized findings that translate technical flaws into quantified business and operational risk.
Field Example: Financial Services — Hidden Lateral Movement Risk
During a recent infrastructure audit for a mid-sized financial institution, our team identified a misconfigured Access Control List that had been overlooked by three previous automated scans. The misconfiguration enabled silent lateral movement between the corporate network and the trading floor segment — a scenario that, if exploited, could have resulted in full domain compromise within hours. The client implemented remediation within 72 hours of our report and passed their subsequent ISO 27001 surveillance audit without findings.

CONTACT US
90% of the businesses who gets hacked
will never be able to recover
Dont Be Next!
GET A QUOTE
Why is penetration testing a strategic necessity for your business?
Penetration testing is essential because it allows organizations to identify and remediate security gaps before real-world attackers can exploit them. Beyond simple automated scanning, our methodology provides a complete adversarial perspective on your environment — demonstrating exactly how a single weak point can escalate into a breach with cascading financial and operational consequences. By exposing these risks early, we help you build the demonstrable security maturity that modern clients, partners, and regulators increasingly demand as a precondition for doing business.
What specific business benefits does our penetration testing provide?
Our penetration testing process is engineered as a strategic instrument designed to reduce business risk while satisfying the highest standards of regulatory compliance.
- Proactive Risk Reduction: We identify unknown vulnerabilities, misconfigurations, and logic flaws across your infrastructure before they can cause service disruption or financial damage.
- Compliance with Global Standards: We deliver documented evidence of compliance with GDPR, HIPAA, PCI-DSS, ISO/IEC 27001, SOC 2, and DORA — supporting audit success and avoiding regulatory penalties.
- Enhanced Team Readiness: We rigorously evaluate how your internal security teams detect and respond to simulated attacks, converting every engagement into a high-value training and tabletop opportunity.
- Evidence-Based IT Spending: Our prioritized findings, ranked by exploitability and business impact, allow management to justify security investment with evidence-based precision and demonstrate ROI to boards.
- Guaranteed Business Continuity: We identify ransomware entry vectors and remote access weaknesses to ensure operational continuity, even under active adversarial pressure.
What is the primary purpose of a CyberSafe penetration test?
The primary purpose is to evaluate your overall security posture by simulating real-world attack chains that reveal the true consequences of a successful breach. Unlike automated tools that may surface a long list of CVEs without context, our experts think like adversaries — chaining together low, medium, and high-severity findings to demonstrate exactly how routine misconfigurations escalate into critical incidents. This process provides leadership with the concrete, scenario-based understanding required to authorize meaningful remediation investment.
Expert Insight: The Human Intuition Advantage
Automated scanners excel at signature-based detection but consistently miss business logic vulnerabilities. In a recent e-commerce engagement, our manual analysis uncovered a payment gateway flaw that allowed negative transaction values to credit customer accounts — a multi-million-dollar exposure invisible to every commercial scanner the client had deployed. This is the difference between detection and discovery.
What specific areas does our penetration testing evaluate?
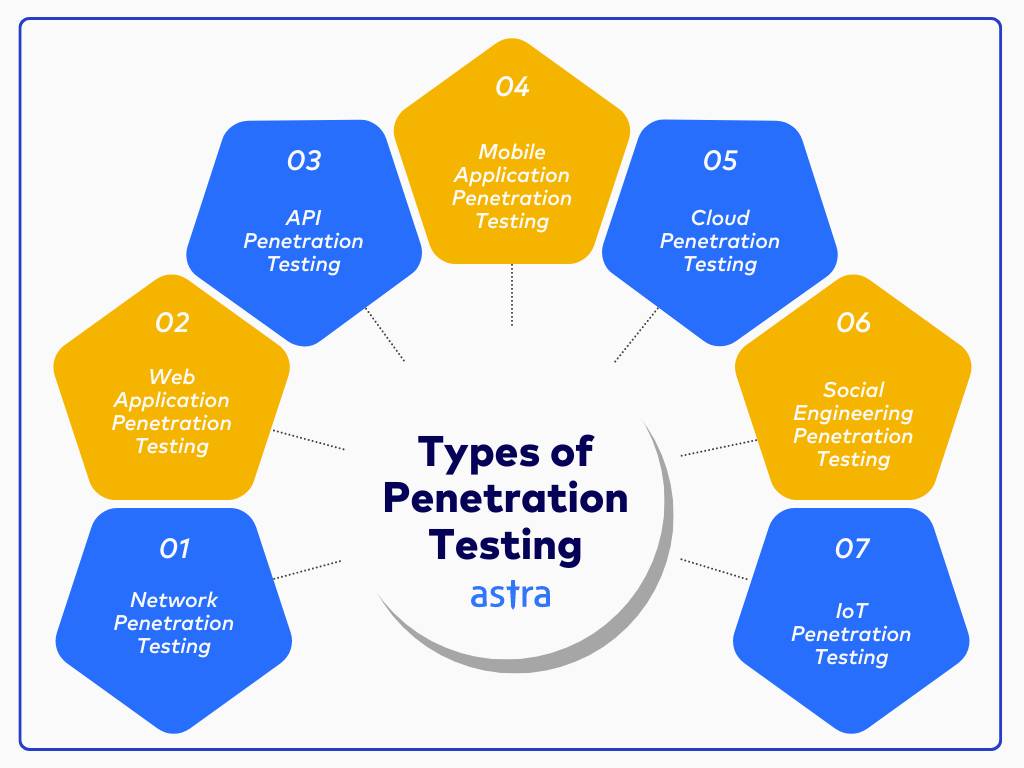
Our penetration testing provides comprehensive coverage of your entire digital and physical attack surface, ensuring every viable entry point is examined under real-world adversarial conditions. We evaluate the resilience of your infrastructure, applications, cloud environments, and human processes to produce a complete map of your organization’s security posture.
- Network Infrastructure: We simulate attacks against internal and external networks — including routers, firewalls, and servers — to identify misconfigured services, exposed ports, and unauthorized access points.
- Web Applications: Our experts target online systems including customer portals, e-commerce platforms, and SaaS applications, applying OWASP Top 10 methodology to uncover injection flaws, broken authentication, and access control failures.
- Mobile Applications: We perform static and dynamic analysis on Android and iOS applications, including reverse engineering and third-party library risk assessment.
- Cloud Security: We evaluate configurations and access controls in AWS, Azure, and Google Cloud environments — including IAM role analysis, exposed APIs, and storage permissions.
- Wireless and LAN: We assess Wi-Fi infrastructure for weak encryption, rogue access points, and risks that enable interception or session hijacking.
- IoT and Smart Devices: We test connected devices — including IP cameras, industrial sensors, and medical wearables — for firmware vulnerabilities and insecure communication protocols.
- Social Engineering: We assess your human firewall through simulated phishing, vishing, and pretexting campaigns to evaluate awareness and procedural enforcement.
- Physical Security: We simulate unauthorized access attempts to restricted areas, testing the resilience of badge systems, access controls, and security personnel protocols.
How does Vulnerability Assessment differ from Penetration Testing — and from?
One of the most common questions we receive from management teams concerns the distinction between vulnerability assessment, penetration testing, and quality assurance. While these disciplines share common ground in identifying defects, they serve fundamentally different purposes and produce different deliverables. Understanding the distinction is essential for budgeting, scoping, and reporting accurately to your board.
Vulnerability Assessment: Breadth and Detection
A vulnerability assessment is a proactive, cost-effective security health check that identifies known weaknesses across your environment through automated scanning combined with expert validation. The objective is breadth: surface as many known vulnerabilities as possible across the broadest possible asset inventory. Vulnerability assessments are ideally conducted continuously or on a monthly cadence, providing the operational telemetry that supports daily security decisions.
Penetration Testing: Depth and Exploitation
Penetration testing is a goal-oriented adversarial simulation that actively exploits vulnerabilities to demonstrate real-world impact. The objective is depth: chain together multiple findings to prove how an attacker would achieve specific outcomes — data theft, privilege escalation, business disruption. Pen tests are typically performed annually, after major changes, or to satisfy specific regulatory requirements.
Quality Assurance: Functionality vs. Security
Quality assurance, while sometimes confused with security testing, has an entirely different focus. QA validates that software and systems function as designed — that buttons work, data flows correctly, and user experiences behave as intended. QA generally does not evaluate whether functionality can be abused, whether trust boundaries can be crossed, or whether authentication can be circumvented. These adversarial questions are the exclusive domain of penetration testing. An application can be functionally flawless and catastrophically insecure at the same time.
How They Complement Each Other
In our experience working with mature security programs, the highest-performing organizations integrate all three disciplines into a continuous assurance cycle. QA validates intended behavior during development. Vulnerability assessments provide continuous monitoring of the production environment. Penetration testing periodically validates that controls actually work against motivated adversaries. Each layer addresses risks the others cannot.
| Scenario | Recommended Approach |
|---|---|
| You want to identify and exploit real-world weaknesses | Penetration Testing |
| You need a broad overview of current system flaws | Vulnerability Assessment |
| You want to validate that software functions as designed | Quality Assurance |
| You’re preparing for an audit or compliance check (ISO 27001, SOC 2, DORA) | Both VA + PT (start with assessment, follow with pen test) |
| You’ve just made a major change to your infrastructure | Both VA + PT |
| You want to train your response teams and validate incident handling | Penetration Testing |
| You’re integrating security into the development lifecycle | All three (QA + VA + PT) |
Case Study: Application Layer Resilience in Fintech
During a recent mobile application assessment for a fintech client, our manual analysis uncovered sensitive session tokens stored unencrypted in the device’s local file system. The client had passed every functional QA test and every automated security scan. Only manual reverse engineering — performed by our certified mobile testers — exposed the issue. The client remediated the flaw before public launch, avoiding what could have become a high-profile breach affecting tens of thousands of end users
What credentials and expertise back our testing team?
The value of a penetration test is determined entirely by the experience and judgment of the testers performing it. At CyberSafe, our consultants hold the most recognized credentials in offensive security, supported by years of hands-on engagement in regulated industries. We do not subcontract our core engagements: every assessment is conducted by senior, certified personnel whose work is reviewed by an independent technical lead.
Our team’s certifications include:
- OSCP (Offensive Security Certified Professional): The industry’s most respected hands-on penetration testing certification, demonstrating practical exploitation capability across modern enterprise environments.
- CEH (Certified Ethical Hacker): Validates comprehensive knowledge of attacker tools, techniques, and procedures aligned with current threat actor behavior.
- CISSP (Certified Information Systems Security Professional): Confirms expertise in information security management, governance, and the broader risk frameworks that pen testing supports.
- CompTIA PenTest+: Compliance-recognized penetration testing certification widely accepted for DoD and government-aligned assessments.
- eWPT and eWPTX: Advanced web application security testing certifications focused on real-world exploitation of modern application stacks.
- Linux Professional Institute Certifications: Recognized credentials in Linux system administration and security operations, foundational for infrastructure testing.
Beyond certifications, our team brings cumulative engagement experience across financial services, healthcare, manufacturing, government, and SaaS — meaning we arrive at every assessment with sector-specific threat intelligence and an understanding of the regulatory context that shapes your priorities.
OUR CERTIFICATIONS






CONTACT US
90% of the businesses who gets hacked
will never be able to recover
Dont Be Next!
GET A QUOTE
What are the primary methodologies used in penetration testing?
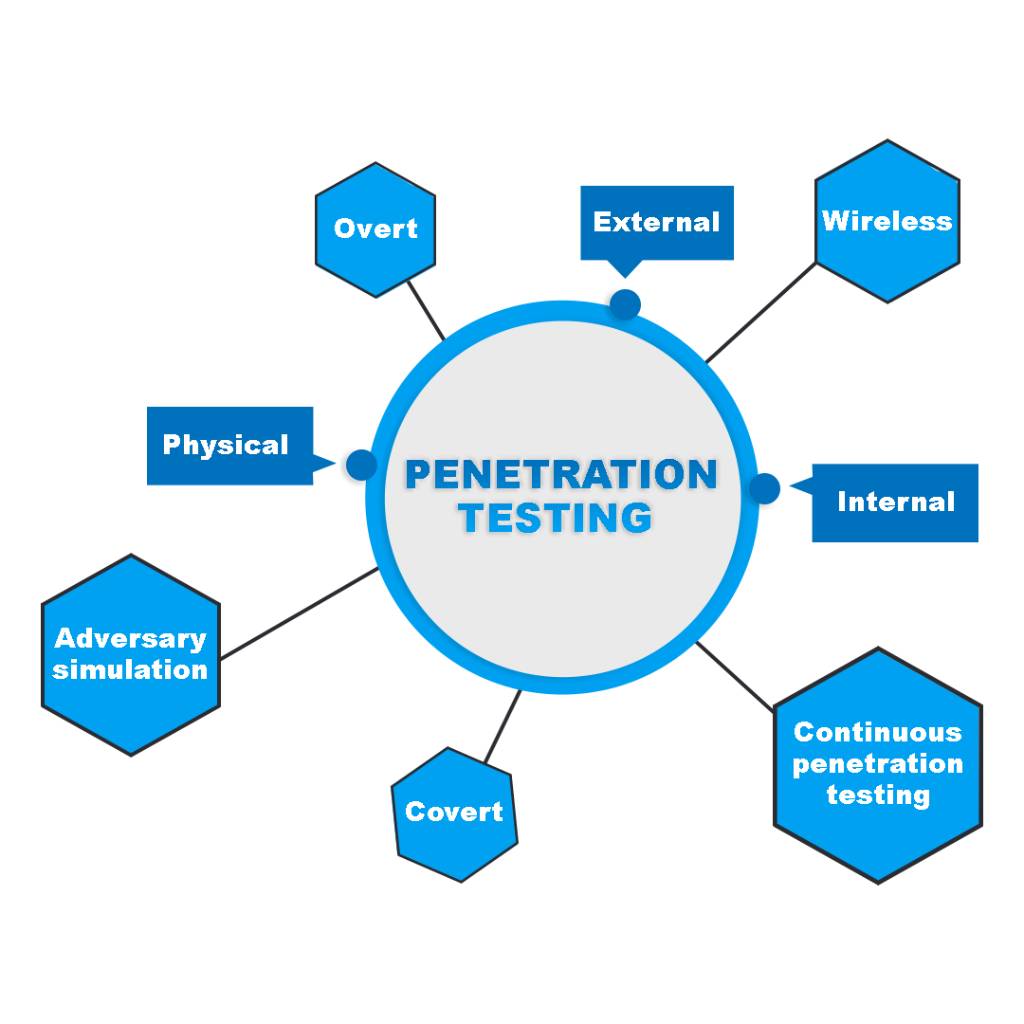
We employ three distinct testing approaches — White Box, Black Box, and Grey Box — to simulate different categories of threat and to satisfy different strategic objectives. Selecting the correct methodology depends on your organization’s specific goals, the systems being tested, your overall risk profile, and the threat scenarios that matter most to your business.
White Box Testing (Clear Box)
White box testing involves providing our experts with full access to the target system’s internal information, including source code, network diagrams, credentials, and architectural documentation.
- Deep Analysis: We perform thorough examination of internal logic and architecture to identify deep-rooted vulnerabilities that external scans systematically miss.
- Insider Threat Simulation: This method accurately emulates the actions of a malicious insider or an advanced persistent threat with significant established knowledge of your environment.
- Strategic Application: Ideal for critical systems, secure development lifecycle integration, and high-value applications where comprehensive code and design review is required.
Black Box Testing (Closed Box)
Black box testing simulates an external attacker who has no prior knowledge of your internal systems. The tester begins with nothing more than what is publicly available.
- Realistic External Perspective: Our team begins the assessment without credentials, source code, or network access — mimicking the conditions of a real-world external adversary.
- Perimeter Evaluation: This approach is optimal for testing public-facing applications and perimeter defenses, measuring exactly how visible and exploitable you appear to motivated outsiders.
Grey Box Testing (Hybrid)
Grey box testing provides our experts with partial knowledge of the system, such as limited credentials or high-level architectural overviews — without full source code disclosure.
- Balanced Efficiency: This approach combines realism with depth, enabling thorough analysis of specific workflows while maintaining an authentic attack simulation.
- User-Centric Testing: This is the most practical engagement model for testing authenticated user-facing systems where some internal access is appropriate but full disclosure is not warranted.
Why is specialized testing critical for web applications?
Web application penetration testing is essential because it identifies application-layer flaws — such as SQL injection, broken authentication, and access control failures — that traditional network security controls cannot detect. Our methodology aligns with OWASP Top 10 and OWASP ASVS, ensuring that customer portals, SaaS platforms, fintech applications, and any web-facing service remain resilient under real-world attack conditions.
What our web application assessment includes:
- Injection and Scripting Analysis: We simulate SQL injection, command injection, and Cross-Site Scripting (XSS) to identify improper input validation and backend exposure.
- Authentication and Session Controls: We test login mechanisms, password reset flows, session management, and privilege escalation paths to ensure unauthorized data access is prevented.
- Business Logic Testing: We identify flaws in user flows — such as bypassing payment steps, manipulating order totals, or chaining multiple discounts — that automated tools fundamentally cannot detect.
- API Security: We probe exposed API endpoints for missing encryption, absent rate limiting, broken authentication, and authorization gaps that increasingly drive real-world breaches.
Expert Insight: Logic vs. Automation
Automated scanners excel at identifying outdated component versions but cannot understand business logic. Our team recently identified a flaw in a retail client’s discount code system that allowed users to stack codes and apply negative values to their balance — a risk no automated tool could have flagged. The fix required no patch and no vendor coordination: it required a human who thought like an attacker
How does mobile application penetration testing protect modern customers?
Mobile application penetration testing identifies security vulnerabilities in Android and iOS apps that traditional QA and functional testing routinely miss. Mobile applications present a unique attack surface because the application itself is distributed to end-user devices — meaning attackers can decompile, instrument, and analyze the application at their leisure. Our assessments simulate real-world attack scenarios that evaluate both internal architecture and runtime behavior, ensuring applications resist tampering, data leakage, and unauthorized backend access.
Our mobile application assessment includes:
- Static and Dynamic Analysis: We review the application’s source or decompiled code while observing its runtime behavior. This dual approach reveals hardcoded secrets, insecure API usage, weak cryptographic implementations, and improper input handling.
- Insecure Data Storage: We examine whether sensitive information — user credentials, authentication tokens, health data, or payment information — is stored unencrypted or in locations accessible to other applications on the device.
- Weak Authentication and Session Handling: We identify weak password policies, missing multi-factor authentication, token reuse vulnerabilities, improper session timeouts, and insufficient protection against brute-force attacks.
- Reverse Engineering Exposure: We test the application’s resistance to reverse engineering tools such as apktool, JADX, Frida, and Hopper — assessing whether internal logic, hardcoded secrets, or API keys can be extracted and weaponized.
- Third-Party Library Risk: We evaluate the open-source libraries, SDKs, and analytics frameworks the application depends on. Third-party components are a leading source of mobile compromise in our assessment data.
- Backend Communication Analysis: We analyze backend interactions to identify insecure communication, weak certificate pinning, missing TLS enforcement, and authentication bypass opportunities.
Case Study: Healthcare Mobile App — Patient Data Exposure
In a recent engagement for a healthcare provider’s patient-facing mobile application, we discovered that authentication tokens were transmitted using a custom protocol that bypassed standard TLS certificate validation. An attacker on a hostile Wi-Fi network could have intercepted these tokens and accessed protected health information for any patient. The vulnerability was invisible to automated mobile scanners because the custom protocol was not recognized as a security control. The client corrected the design within their next release cycle, preserving HIPAA compliance and avoiding potential disclosure to regulators
What is the role of network and infrastructure penetration testing?
Network and infrastructure penetration testing is a comprehensive adversarial evaluation of your internal and external IT assets — including servers, routers, switches, firewalls, VPN gateways, and connected endpoints. We simulate realistic attack scenarios against your core infrastructure to assess how misconfigured services, outdated operating systems, or weak segmentation could allow an intruder to gain a foothold, escalate privileges, and move laterally. Our process aligns with the MITRE ATT&CK framework, ensuring every viable path for compromise is identified and documented.
What our infrastructure assessment includes:
- Network Enumeration: We map your network, identify active IP ranges, enumerate open ports, and catalog running services on every reachable host.
- Firewall and ACL Testing: We evaluate access control lists, firewall rule sets, and segmentation policies to detect misconfigurations that enable unauthorized traffic flow between zones.
- Active Directory Security: We analyze your Active Directory configuration to uncover paths that could lead to Domain Controller compromise — a leading vector in ransomware incidents.
- Privilege Escalation Analysis: We assess permission structures to detect misconfigurations that allow unauthorized users to gain elevated access.
- Communication Security: Our experts evaluate whether network traffic is properly encrypted to protect against interception or data leakage.
- Protocol and Service Analysis: We identify outdated or insecure services and protocols, such as SMBv1, Telnet, or unpatched RDP, that expose your environment to known exploitation.
- Logging and Detection Review: We verify whether your SOC or SIEM detects and alerts on suspicious activity during the engagement — measuring your real detection capability, not your stated capability.
- DDoS Resilience: We check your infrastructure’s capacity to withstand or mitigate denial-of-service attacks aimed at disrupting critical services.
Why does wireless network penetration testing remain essential?
Wireless network penetration testing targets your organization’s Wi-Fi infrastructure to identify misconfigurations, weak encryption, and vulnerabilities that could enable unauthorized access or sensitive traffic interception. Wireless remains one of the most underestimated attack vectors in enterprise security: a single rogue access point or weakly authenticated guest network can provide direct bypass of every perimeter defense your organization has invested in.
Our wireless assessment includes:
- Rogue Access Point Detection: We identify unauthorized or misconfigured wireless devices broadcasting on or near your premises — including employee-installed personal hotspots that bypass corporate controls.
- Encryption and Authentication Testing: We evaluate the security of WPA2-Enterprise, WPA3, and 802.1X implementations, including credential exposure analysis and certificate validation testing.
- Eavesdropping Simulation: We attempt to intercept wireless traffic and extract sensitive information such as authentication credentials, session tokens, or internal communications.
- Evil Twin and SSID Spoofing: We test how susceptible your users are to connecting to fraudulent networks that mimic trusted corporate SSIDs — a leading vector for credential theft in mobile workforces.
- Guest Wi-Fi Segregation: We verify that guest networks are properly isolated from internal systems, preventing lateral movement from public Wi-Fi into the corporate environment.
- Physical and RF Boundary Analysis: We assess physical access controls and signal leakage beyond the property perimeter, identifying opportunities for attackers operating from adjacent buildings or parking areas.
Case Study: Manufacturing — Rogue Access Point Compromise
During a wireless assessment for a manufacturing client, our team discovered a rogue access point installed by a contractor working in the production area. The device provided unfiltered access to the operational technology network from the public parking lot. While the client’s perimeter firewall was robust, this rogue device circumvented every layer of network defense. We worked with the client to implement continuous wireless monitoring and updated contractor access policies, closing a vector that had remained open for at least six months.
Why is IoT security testing critical for modern enterprises?
IoT penetration testing identifies vulnerabilities in connected devices — smart sensors, IP cameras, medical wearables, building automation systems, and industrial controllers — that frequently lack native security. Because these devices operate with limited computing resources and often unpatched firmware, they are favored targets for attackers seeking persistent footholds and lateral pivot opportunities. We evaluate the entire ecosystem, from physical hardware through cloud integrations and supporting mobile applications.
Our specialized IoT assessment covers:
- Firmware Reverse Engineering: We analyze device firmware to discover hardcoded credentials, insecure configurations, weak cryptographic implementations, and undocumented backdoor features.
- Device Communication Analysis: We intercept and inspect data transmissions across Bluetooth, Zigbee, MQTT, and Wi-Fi to identify unencrypted traffic, weak authentication, and insecure backend APIs.
- Remote Access and Interface Testing: We evaluate access controls for web dashboards, mobile companion apps, and remote management interfaces associated with each device.
- Physical Security Checks: We assess whether physical tampering — such as accessing exposed debug ports, JTAG, or UART — could enable data extraction, privilege escalation, or device control override.
- Cloud and Mobile Integration Testing: We review the device’s interaction with cloud services and companion applications to identify weaknesses in data storage, user management, and backend APIs.
Case Study: Industrial IoT — Production Floor Exposure
In an assessment for an industrial automation client, we identified that smart sensors deployed across the production floor used hardcoded credentials documented in publicly available manufacturer manuals. An attacker reaching the device network — perhaps via the wireless or vendor-access vectors above — could have shut down production lines or manipulated quality control sensors to produce defective output undetected. The client deployed network segmentation and a credential rotation program based on our recommendations, materially reducing operational risk.
How does social engineering testing protect your human firewall?
Social engineering testing evaluates your organization’s security culture by simulating the deception tactics that real adversaries use to manipulate employees into granting unauthorized access. Unlike technical testing, this assessment targets human behavior and adherence to security policy. Our goal is to identify weaknesses in training, procedure, and awareness before a malicious actor exploits them — recognizing that even the strongest technical controls can be circumvented by a single successful phishing attempt.
- Phishing and Vishing Campaigns: We design custom email and phone-based simulations to measure how susceptible your team is to credential theft, malicious link clicks, and pretext-based information disclosure.
- Physical Intrusion Simulation: Our red team operatives attempt to gain unauthorized entry to restricted areas using tactics such as tailgating, vendor impersonation, and pretext-based access requests.
- USB Drop Testing: We place simulated malicious drives in employee-accessible areas to evaluate the risk of curiosity-driven malware execution.
- Awareness and Policy Compliance: We observe whether employees report suspicious activity, follow clean desk policies, and adhere to badge and access control procedures during the engagement window.
Expert Insight: Security is a Management Responsibility
In a recent engagement, we discovered that while the client’s network was robust, a simulated vendor impersonation allowed our operative to gain physical access to the server room within forty minutes of arriving on site. The technical controls were excellent. The procedural controls had not been tested in three years. This insight allowed the client to implement stricter physical access controls, vendor verification protocols, and quarterly tabletop exercises with reception staff.
How does physical penetration testing secure your critical infrastructure?
Physical penetration testing evaluates the resilience of your facility’s access protocols by simulating unauthorized attempts to enter restricted zones such as data centers, server rooms, and executive areas. We employ red team tactics — including social engineering, stealth observation, and specialized tools — to bypass physical security controls including keycards, biometric scanners, and electronic locks. This process identifies vulnerabilities that threat actors might exploit for corporate espionage, intellectual property theft, or hardware compromise.
Our physical assessment includes:
- Access Control Bypass: We attempt to circumvent PIN pads, electronic locks, and physical barriers through techniques such as lock picking, tailgating, and procedural exploitation.
- RFID and Badge Security: Our experts test for vulnerabilities in badge systems, including the potential for cloning, skimming, or replay attacks on RFID-based access cards.
- Physical Device Tampering: We assess the feasibility of installing rogue devices — such as network taps, USB keyloggers, or wireless implants — within office environments.
- Sensitive Document Recovery: We examine discarded documents, hardware, and storage devices for unshredded sensitive information that could reveal internal processes, passwords, or business plans.
CONTACT US
90% of the businesses who gets hacked
will never be able to recover
Dont Be Next!
GET A QUOTE
What methodology ensures a successful and transparent penetration test?
Our methodology follows a rigorous seven-stage process aligned with NIST SP 800-115, OWASP, and MITRE ATT&CK to deliver a results-driven evaluation of your security posture. We combine automated scanning with deep manual analysis to move beyond theoretical risk and demonstrate concrete business impact.
- Scoping and Planning: We define the systems to be tested, the rules of engagement, and the boundaries of the assessment based on your risk profile and compliance requirements.
- Reconnaissance: Our experts gather intelligence on your infrastructure — both passively through open sources and actively through scanning — mapping your attack surface as an adversary would.
- Vulnerability Analysis: We identify gaps in your network, applications, and infrastructure using a combination of manual techniques and advanced toolsets.
- Exploitation: We safely attempt to exploit identified vulnerabilities in a controlled manner to determine their actual impact, not just their theoretical severity.
- Post-Exploitation: We mimic lateral movement, credential harvesting, and persistence techniques to demonstrate how far an attacker could go after initial access.
- Reporting: We deliver a clear, prioritized report containing both an executive summary and detailed technical remediation steps written in plain language.
- Retesting: We verify that your implemented fixes are effective, that previously exploited paths are closed, and that no new vulnerabilities were introduced by the remediation itself.
Understanding the 5-Stage and 8-Stage Frameworks
Different professional frameworks describe penetration testing through five, seven, or eight discrete stages. These are not contradictions — they reflect different levels of granularity for different audiences. For management reporting, the 5-stage view is generally sufficient. For technical execution and compliance documentation, the 8-stage view provides the necessary detail.
The 5 Core Stages (Management View)
- Planning and Preparation: Defining scope, goals, and rules of engagement with full stakeholder alignment.
- Information Gathering (Reconnaissance): Quietly collecting target information as an external attacker would.
- Enumeration and Vulnerability Analysis: Cataloging systems, services, and identifying exploitable weaknesses.
- Exploitation: Actively exploiting identified findings to prove real-world impact.
- Reporting and Remediation: Delivering prioritized findings with actionable remediation guidance.
The 8 Detailed Stages (Technical View)
The 8-stage framework expands the technical workflow further, separating reconnaissance into distinct passive and active phases and breaking out post-exploitation and remediation verification as standalone stages:
- Reconnaissance: Define objectives, scope, and rules of engagement.
- Scanning: Identify open ports, services, and potential vulnerabilities.
- Enumeration: Build on scanning results to gather detailed system data.
- Vulnerability Analysis: Analyze findings to identify exploitable weaknesses and prioritize effort.
- Exploitation: Simulate attacks against identified vulnerabilities.
- Post-Exploitation: Assess how far an attacker could penetrate and what access could be maintained.
- Reporting: Document findings with risk prioritization and remediation guidance.
- Remediation Verification: Conduct follow-up testing to confirm vulnerabilities have been effectively addressed.
What tools and platforms does our penetration testing team employ?
Effective penetration testing depends on a carefully curated toolkit that supports each phase of the engagement — from reconnaissance through exploitation to reporting. While tools are never a substitute for experienced testers, the right toolkit dramatically improves coverage, accuracy, and efficiency. Our team utilizes the same platforms employed by real-world threat actors, ensuring that every assessment reflects current adversarial reality.
Reconnaissance and Network Mapping
- Nmap: The industry-standard tool for network discovery, port scanning, and service enumeration. We use Nmap to map active hosts, identify exposed services, and detect potentially vulnerable software versions.
- Amass: An advanced asset discovery and subdomain enumeration platform used for comprehensive external reconnaissance.
- Shodan and Censys: Used for OSINT gathering and identification of exposed internet-facing assets.
Vulnerability Assessment
- Nessus: A leading vulnerability scanner that identifies known security issues across systems, supports compliance scanning, and supports risk-based prioritization.
- OpenVAS and Qualys: Open-source vulnerability assessment platform used for cross-validation and specialized scanning scenarios.
- Nikto: A focused web server scanner for identifying outdated software, dangerous misconfigurations, and default credentials.
Exploitation and Post-Exploitation
- Metasploit Framework: The leading framework for developing and executing exploits in controlled environments — supporting validation of vulnerability severity and post-exploitation simulation.
- BloodHound: Visualizes and analyzes Active Directory permissions and relationships to identify attack paths leading to Domain Admin compromise.
- Hydra and Medusa: Tools used for brute-force credential testing across multiple protocols including SSH, FTP, and RDP.
- John the Ripper and Hashcat: Industry-standard password cracking tools used to test password strength and exposed credential hashes.
Web Application Testing
- Burp Suite Professional: The defining platform for web application security assessment — supporting intercepting proxy analysis, automated scanning, brute-force testing, and session manipulation.
- SQLMap: Automated tool for detecting and exploiting SQL injection vulnerabilities across diverse database platforms.
- OWASP ZAP: Open-source web application scanner used as part of our defense-in-depth testing methodology.
Wireless and Network Analysis
- Aircrack-ng: Comprehensive suite for auditing wireless networks, including WPA/WPA2 capture and analysis.
- Wireshark: Protocol analyzer that captures and inspects packets in real time, enabling detection of sensitive data transmitted over unencrypted channels.
Mobile and Specialized Testing
- Frida and Objection: Dynamic instrumentation toolkit used for runtime manipulation of mobile applications.
- JADX and apktool: Decompilation and static analysis tools for Android applications.
How do manual expertise and automated tools combine in our methodology?
One of the most important strategic decisions in penetration testing is the balance between manual expertise and automated scanning. Vendors that rely exclusively on automated tools deliver low-cost reports with limited insight. Manual testing alone is too slow and expensive to achieve broad coverage. The right answer — and the approach we have refined across years of engagement — combines both in deliberate proportion.
What Automated Tools Do Well?
Automation excels at breadth. Within hours, automated scanners can enumerate ports across thousands of hosts, identify known CVEs, fingerprint outdated software versions, and surface obvious misconfigurations. For known vulnerabilities with established signatures, automated tools are fast, reliable, and inexpensive.
What Only Humans Can Do?
Manual testing excels at depth and creativity. Human testers can chain together multiple low-severity findings into a critical exploit, identify business logic flaws unique to your application, recognize patterns that suggest insecure design choices, and adapt their tactics in response to discoveries made during the engagement. Most importantly, human testers can think like attackers — questioning assumptions, identifying trust boundaries, and probing the edges of what the system was designed to permit.
Where Custom Tooling Matters?
In some engagements, off-the-shelf tools are insufficient. Our team develops custom scripts and payloads to simulate advanced attacks or bypass layered defenses. This is especially common in mobile application testing — where custom API fuzzers may be required — and IoT testing, where firmware analysis often demands bespoke instrumentation. The capacity to develop tooling on demand is a meaningful differentiator between commodity vendors and serious testing practices.
What are the honest pros and cons of penetration testing?
We believe transparency is a precondition of trust. Penetration testing is a powerful instrument, but it is not magic, and management deserves an honest assessment of what it can and cannot deliver. Below is our candid view of the advantages and limitations of the discipline.
Strengths and Benefits
- Identifies Critical Vulnerabilities: Penetration testing provides a real-world perspective on security gaps that compliance checklists and theoretical risk assessments cannot match.
- Enhances Security Posture: Engagement findings drive specific, prioritized improvements to defenses against advanced threats — meaningful security investment rather than security spending.
- Customizable to Your Context: Every engagement can be tailored to the specific systems, threats, and business objectives that matter most to your organization.
- Compliance and Certification: Documented penetration testing supports compliance with ISO 27001, SOC 2, DORA, HIPAA, PCI-DSS, and most major frameworks.
- Executive and Board Reporting: By measuring real adversarial capability, pen testing produces evidence-grade documentation for boards, insurers, and acquiring organizations during due diligence.
Limitations and Considerations
- Cost: High-quality penetration testing requires senior expertise, which translates into meaningful cost. We always recommend prioritizing scope and depth over volume.
- Time Investment: Thorough analysis and reporting requires meaningful time — typically two to six weeks for an enterprise engagement, depending on scope.
- Point-in-Time Insight: Every penetration test is a snapshot of a single point in time. Continued security demands ongoing assessment, not a single annual event.
- Potential for Disruption: If not carefully scoped and coordinated, testing can occasionally affect production systems. This is why scoping, rules of engagement, and communication protocols matter so much.
- Cannot Guarantee Complete Security: A penetration test cannot guarantee that all vulnerabilities have been found, nor that fixes will be implemented effectively. It is a critical input to a broader security program, not a replacement for one.
Can penetration testing guarantee complete security?
This is one of the most important questions a security leader can ask — and we believe in answering it directly. No, penetration testing cannot guarantee complete protection against all threats. Any vendor that claims otherwise is either misrepresenting the discipline or has misunderstood it. Penetration testing identifies vulnerabilities present at a specific moment in time, within a specific scope, against the techniques known to the testing team. New vulnerabilities emerge continuously, new attack techniques evolve, and your own environment changes weekly through software updates, new integrations, and personnel changes.
What penetration testing does provide — when conducted properly and integrated into a broader security program — is the highest-confidence evidence available that your defenses meaningfully resist real-world attack. It identifies systemic weaknesses, demonstrates exploitable impact, validates the effectiveness of your existing controls, and provides prioritized remediation guidance. Combined with continuous monitoring, vulnerability management, security awareness training, and incident response readiness, penetration testing forms a cornerstone of mature cybersecurity — not its entirety.
Our recommendation to every client is consistent: treat penetration testing as the validation layer of a defense-in-depth program, not as the program itself. Conduct testing at meaningful frequency, act decisively on findings, and measure the trajectory of your security maturity over time. Done this way, penetration testing delivers exactly what executives need from cybersecurity: not perfection, but defensible, evidence-based confidence.
What is the strategic roadmap following a penetration test?
The true value of a penetration test lies in the remediation phase, where we help you prioritize risks and improve your long-term security architecture. Once the report is delivered, our team provides the managerial oversight necessary to ensure that technical findings translate into actionable business resilience.
- Risk Prioritization: We help you focus on the most urgent vulnerabilities based on exploitability, business damage potential, and regulatory exposure.
- Remediation Guidance: Our experts provide hands-on support for configuration changes, patching strategy, and code-level fixes — collaborating directly with your IT teams.
- Compliance Mapping: We map findings to specific regulatory controls under DORA, ISO 27001, SOC 2, HIPAA, and PCI-DSS, making subsequent audits substantially easier to manage.
- Retesting for Validation: We perform follow-up tests to confirm that previously exploited paths are now fully secured and that remediation did not introduce new exposures.
- Long-Term Architectural Guidance: Beyond tactical fixes, our security consultants offer strategic recommendations to improve your overall security architecture, monitoring posture, and incident response readiness.
Expert Insight: Beyond the Report
A penetration test is not a one-time event — it is a critical component of your cybersecurity roadmap. We recommend conducting assessments at least annually, after any major infrastructure change, before product or system launches, and following any security incident. Mature organizations build penetration testing into their cybersecurity calendar with the same discipline they apply to financial audits.
Strategic security is a management function, not a technical checklist. At CyberSafe, we take responsibility for your organization’s resilience — ensuring you stay ahead of both evolving threats and intensifying regulatory expectations.
IS YOUR BUSINESS REALLY NEED A PENETRATION TEST?
CyberSafe Security is a leader in Penetration Testing and Vulnerability Assessment.
We’ve been providing advanced security testing services since 2003; testing hundreds of companies
to validate and confirm that their business-critical objectives and information are safe.
As an industry leader, we are committed to maintaining the highest levels of training and certifications for all our security testing experts.
Our penetration tests use both automated tools developed in-house, as well as well-known industry tools.
Schedule a Professional Consultation with Our Certified Penetration Testing Team
Professional FAQ: Penetration Testing Insights
How often should we perform penetration testing?
We recommend at least once a year as a baseline, with additional engagements triggered by major changes such as cloud migration, new application launches, or post-incident review. High-risk environments — including finance, healthcare, and critical infrastructure — frequently benefit from semi-annual or rolling assessment programs.
What is the difference between a penetration test and a vulnerability assessment?
A vulnerability assessment identifies known flaws through automated scanning and expert validation, providing breadth. A penetration test involves manual exploitation to measure real-world business impact, providing depth. The most mature programs employ both — vulnerability scanning on a continuous cadence and penetration testing periodically.
Is penetration testing the same as quality assurance?
No. QA validates that software functions as designed; penetration testing validates that software resists abuse by motivated adversaries. An application can pass every QA test and remain critically insecure. These disciplines are complementary, not interchangeable.
Will a penetration test affect our business continuity?
When properly scoped and coordinated, no. We work closely with your IT and operations teams to define rules of engagement, exclusion windows, and communication protocols that ensure simulations are conducted safely without disrupting production environments.
Does our organization need a penetration test for SOC 2 or ISO 27001 compliance?
Yes. While the methodologies described vary by framework, both SOC 2 and ISO 27001 require demonstrable evidence of ongoing security assessment to validate the effectiveness of your controls. DORA, HIPAA, and PCI-DSS impose similar expectations within their respective domains.
What qualifications should a penetration tester have?
Reputable penetration testers hold recognized credentials such as OSCP, CEH, CISSP, or PenTest+, complemented by demonstrable hands-on experience in your specific industry context. We strongly recommend evaluating providers based on the experience and certifications of the individuals who will actually perform your engagement, not just the company’s marketing materials.
Can penetration testing guarantee complete security?
No. Penetration testing identifies vulnerabilities and meaningfully improves your security posture, but it cannot guarantee complete protection against all threats. It is the most reliable validation layer available, but it must be combined with continuous monitoring, vulnerability management, and incident response readiness to form a complete cybersecurity program.
What happens if the test discovers a critical vulnerability?
We immediately flag critical findings to your designated management contact, allowing for rapid remediation before the full report is even finalized. For severe issues, we provide same-day notification and remediation guidance. Critical findings are never held until the formal report — they are escalated in real time.
How is the engagement priced?
Pricing depends on scope — the systems to be tested, the methodologies applied, and the depth required. We provide fixed-fee proposals based on a scoping conversation, ensuring no surprises and predictable budget alignment. We always recommend prioritizing scope and depth over volume.
What deliverables will we receive?
Every engagement concludes with a comprehensive deliverable package including an executive summary written for management, a detailed technical report with proof-of-concept evidence, a prioritized remediation roadmap, and an attestation document suitable for sharing with auditors, customers, and regulators.

