TanStack npm Packages Compromised in Ongoing Mini Shai-Hulud Supply-Chain Attack
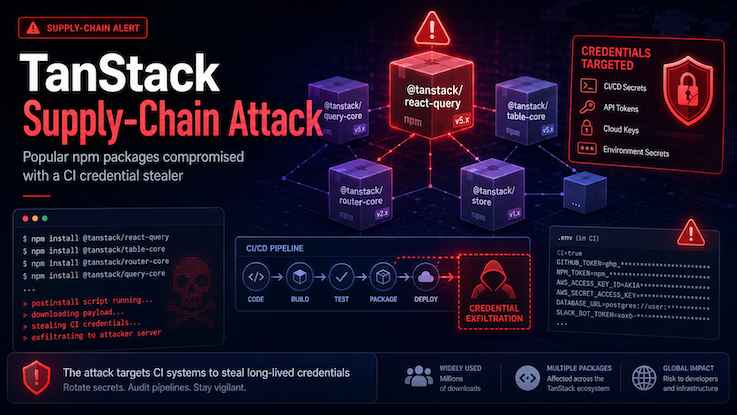
The Socket Threat Research team detected a major compromise affecting 84 npm package artifacts under the TanStack namespace. Several of the impacted packages are extremely popular, including @tanstack/react-router, which reportedly receives over 12 million weekly downloads.
The compromised versions were modified to include a suspicious file named router_init.js, believed to be a credential stealer targeting CI/CD environments, especially GitHub Actions. The malware appears designed to access sensitive GITHUB* environment variables, including tokens and actor identity data, which could expose build secrets and enable further supply-chain compromise.
The added file was unusually large, around 2.3 MB, and heavily obfuscated using patterns commonly associated with malicious JavaScript, including string-array rotation, hex-encoded lookups, control-flow flattening, dead-code injection, and daemonized background execution. It also showed behavior consistent with staging files in temporary directories and remotely dispatching collected data.
Socket’s AI Scanner flagged all malicious package versions within six minutes or less after publication, highlighting both the severity of the incident and the importance of real-time software supply-chain monitoring.
Why this matters
Because TanStack packages are widely used directly and transitively across modern JavaScript applications, this compromise could affect a broad range of development pipelines. Organizations using affected versions should immediately review dependency versions, rotate exposed CI/CD secrets, audit GitHub Actions activity, and scan build environments for suspicious behavior.
The full list of compromised packages is available at the link below
https://socket.dev/blog/tanstack-npm-packages-compromised-mini-shai-hulud-supply-chain-attack


